
Cybersecurity technology mixes up memory to thwart attacks
A new cybersecurity technology recently licensed from Lincoln Laboratory is taking on one of today's most pervasive vulnerabilities: memory corruption. Memory corruption bugs are used by attackers to inject malicious code into a computer system, in such a way that gives attackers control of a system or the ability to steal data. These attacks are especially dangerous because they can compromise millions of computers at once.
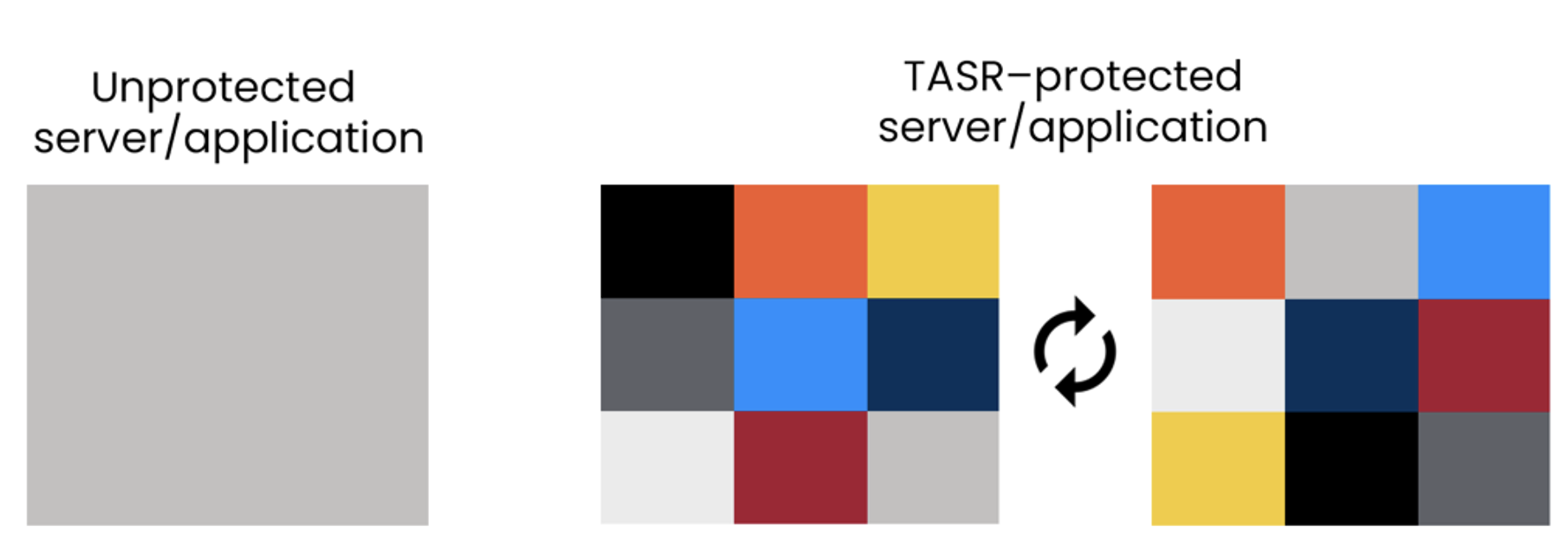
The technology, called Timely Address Space Randomization (TASR), protects against these attacks in Linux applications and servers by shuffling around, or rerandomizing, the location of code in memory. Like an unbeatable game of whack-a-mole, this moving-target technique makes it extremely difficult for hackers to locate the vulnerabilities they usually exploit in such an attack.
The technology has been licensed by InfoSiftr, a software company whose focus is on securing applications for cloud deployment.
"We have worked hard since the inception of TASR to make it a practical defense with minimal impact on user experience; paired with the protection it offers, this has contributed to its successful transition,” says Hamed Okhravi, a senior researcher in Lincoln Laboratory's Secure Resilient Systems and Technology Group. Okhravi invented TASR at the Laboratory with David Bigelow, Thomas Hobson, Robert Rudd, and William Streilein.
Memory corruption vulnerabilities are some of the most prevalent foibles out there; a 2019 Microsoft study found that they accounted for nearly 70% of all vulnerabilities in their products. Protections exist today, but these solutions still leave gaps for attackers to exploit. One of the most popular solutions, called address space layout randomization (ASLR), uses a similar premise as TASR of randomizing memory layout. However, ASLR randomizes memory just once, an approach which attackers have worked around by using "information-leakage attacks." In these attacks, hackers force an application to disclose how its memory has been randomized, undoing the impact of the randomization.
TASR guards against information leakage by automatically randomizing the layout of code in memory every time it observes an output by an application. "By rerandomizing the memory locations of all code pieces every time any output is generated, TASR renders leaked information stale and resists attacks that can otherwise bypass randomization defenses," Okhravi says.
TASR only takes minutes to install on a machine and is seamless to operate after the installation. Performance evaluations by the Laboratory development team showed that the TASR technique incurs an average 2% increase in execution time in common Linux servers and applications — a delay that is often masked by normal execution lags and is not noticeable to users. Since Linux is widely used in servers, cloud settings, and super computers, this technology provides an effective protection for large sectors of users.
To prepare TASR for transition to government or industry use, the development team worked with the Department of Homeland Security's Commercialization Accelerator Program, in addition to the Laboratory's Technology Ventures Office and MIT's Technology Licensing Office.