Projects

systems analysis
Wildfire Working Group
A group of non-profit organizations joined forces to assess the nation’s wildfire crisis and provided key recommendations.
Tags

CrisisChat
An emergency response chatbot aims to enable centralized and reliable communications between the public and first responders.
Tags

Translating All C To Rust (TRACTOR) Benchmarks
Lincoln Laboratory is leading test and evaluation on a DARPA program to translate large C codebases into memory-safe Rust code, releasing a benchmark every six months to guide program performers.
Tags
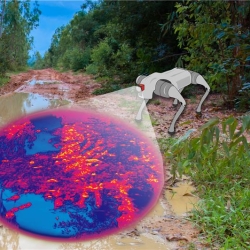
HYPE2GO: Cost Maps from Hyperspectral Imaging
The HYPE2GO project seeks to augment autonomous system terrain understanding with hyperspectral imaging.
Tags
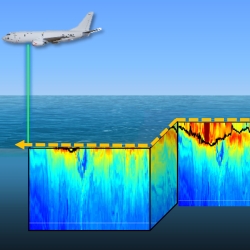
Measuring Subsurface Ocean Properties from the Air
A sensor capable of rapidly collecting high-resolution data on ocean temperature, salinity, and sound speed remotely could improve forecasting for defense missions.
Tags
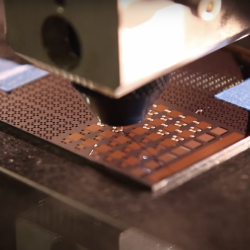
Low-Temperature Additive Manufacturing of Glass
An innovative approach to additive manufacturing of multimaterial glass items precludes the need for costly high-temperature processing techniques.
Tags

KREMS Technology Rearchitecting
A complete rearchitecting of radar backends will enable the missile and space missions on Kwajalein for decades to come.
Tags

Secure Radios for Uncrewed Systems
A security module, pre-certified by the National Security Agency, for protecting communications on uncrewed platforms can accelerate the fielding of new systems and open opportunities for the commercial sector.
Tags
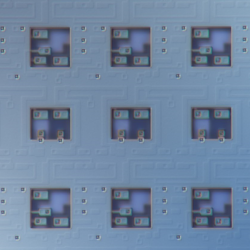
Superconducting Content-Addressable Memories (SuperCAMs)
Unconventional memory circuits can accelerate data processing in cyber sensing devices by reducing the latency of matching complex data patterns to specialized processing pipelines.
Tags
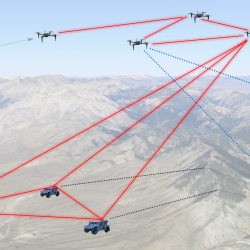
Precision Clock Synchronization for Advanced Sensing
Combined quantum networking and lasercom optical signaling techniques could impact advanced sensing applications such as geolocation with distributed systems.
Tags