
Cyber Operations and Analysis Technology
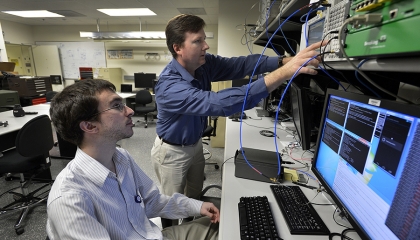
The Cyber Operations and Analysis Technology Group is dedicated to real-world impact in the cyber domain. We research complex technical problems, develop groundbreaking technologies, and prototype systems that directly address national security challenges. Our goal is to improve cybersecurity, enhance operational effectiveness, and deliver measurable results for our sponsors.
We work across a variety of cutting-edge national security applications to
- Enhance the cybersecurity and resiliency of critical infrastructure and other operational technology
- Equip the nation’s cyber operators with technology to execute their missions more effectively, more efficiently, and at scale
- Assess and quantify risk posed by adversary cyber threats to key national security missions
- Develop advanced analytics and processing techniques to generate timely, actionable insights from cyber data
Featured Projects
computing
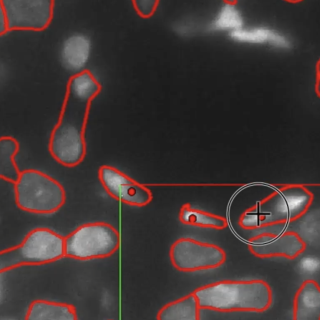
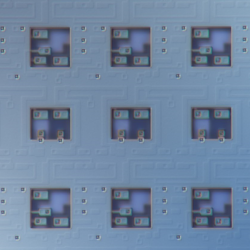
Superconducting Content-Addressable Memories (SuperCAMs)
Unconventional memory circuits can accelerate data processing in cyber sensing devices by reducing the latency of matching complex data patterns to specialized processing pipelines.

cyber security
Applied Resilience for Mission Systems
We’re improving and guiding the resilience of Department of War missions by adapting commercial practices and academic research for the development, operation, and sustainment of software-intensive systems.
Latest News
Laboratory Stories
My career thus far has largely been influenced by the fact that the Laboratory has given me a lot of freedom in which projects and topics I’ve focused on, allowing me to carve my own path.
Jessica Ray
Computer Scientist
Cyber Security and Information Sciences
Cyber Operations and Analysis Technology
Advancing Our Research
Featured Publications
Toward improving EN adoption: Bridging the gap between stated intention and actual use
Jun 3
MIT Lincoln Laboratory Report ACTA-7
Beyond expertise and roles: a framework to characterize the stakeholders of interpretable machine learning and their needs
Jan 24
Proc. Conf. on Human Factors in Computing Systems, 8-13 May 2021, article no. 74.
Towards a distributed framework for multi-agent reinforcement learning research
Sep 22
2020 IEEE High Performance Extreme Computing Conf., HPEC, 22-24 September 2020.
Our Staff
View the biographies of members of the Cyber Operations and Analysis Technology Group.