Cyber System Assessments
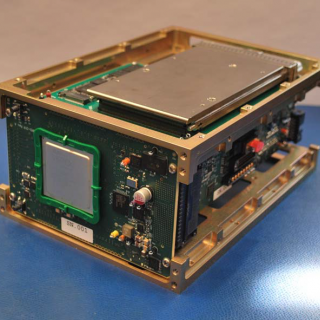
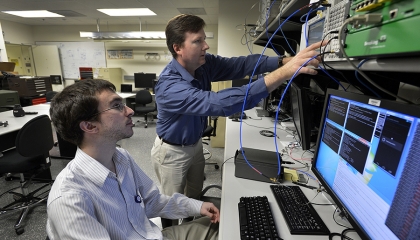
Our team discovers novel vulnerabilities in systems ranging from computers and cellphones to cars and jet fighters. In order to improve the defenses of systems, we use reverse engineering to find ways to maintain control over hardware and software. We coordinate with the Department of Defense and Intelligence Community to evaluate cyber defense systems and enable effective cyber operations.
Featured Projects

sensing
Private Automated Contact Tracing
An automated, Bluetooth-based system helps perform contact tracing in a private, anonymous way, offering a method to reduce disease spread during a pandemic.

cyber security
Large-scale Automated Vulnerability Addition
Computer scientists can test techniques for finding vulnerabilities in code.

cyber security
PANDA – Platform for Architecture-Neutral Dynamic Analysis
An open source platform helps analysts quickly reverse engineer large, real-world binary systems to better analyze how software executes.
Latest News
Laboratory Stories
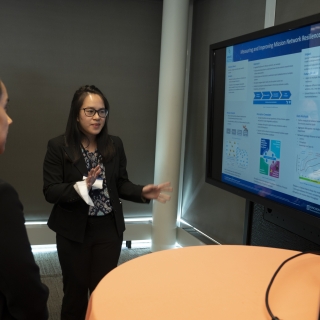
I have enjoyed expanding my cyber defense skills for national security research.
Madeline McLaughlin
Cyber Systems Exploitation Researcher
Cyber Security and Information Sciences
Cyber System Assessments
Advancing Our Research
Featured Publications
Artificial intelligence: short history, present developments, and future outlook, final report
Jan 1
MIT Lincoln Laboratory Report
Mission assurance: beyond secure processing
Jul 16
18th IEEE Int. Conf. on Software Quality, Reliability, and Security, QRS 2018, 16-20 July 2018, pp. 593-8.
SoK: privacy on mobile devices - it's complicated
Mar 2
Proc. on Privacy Enhancing Techn., Vol. 3, 2016, pp. 96-116.