Cyber technologists talk national security
Lincoln Laboratory held its Cyber Technology for National Security (CTNS) conference from June 28 to 29. The annual event provides a forum to discuss the latest cyber technology research and its application to national security problems.
Last year, an Executive Order on Improving the Nation’s Cybersecurity called for bold changes to better defend the computer systems that “underpin the American way of life.” Modernizing cybersecurity practices, strengthening the detection of attacks, and improving collaboration on cyber research are key goals of the order. These themes ran through the nearly 30 talks on the CTNS agenda, many of which presented the new prototypes developed in the Laboratory’s Cyber Security and Information Sciences Division for transitioning to the Department of Defense (DoD).
"Our nation is heavily dependent on cyber systems, with every service having a multitude of computer-based capabilities," says CTNS chair Douglas Stetson. "These systems need to continue to operate to accomplish their mission, even in the face of cyberattack. We also need to recognize when we are under cyberattack and take counter actions to protect systems."
More than 200 people attended the event, many representing the U.S. government and federally funded research and development centers.
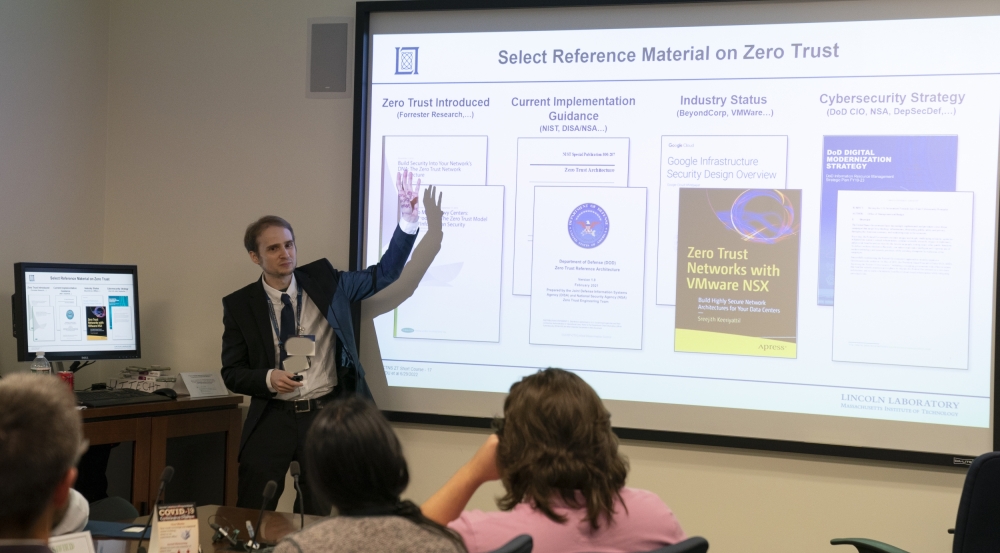
Implementing zero-trust security
Several talks at CTNS described technology to support zero-trust (ZT) principles, the idea that users or devices should not be implicitly trusted just because they are authorized to be inside of a network. In recent years, ZT security has been a growing focus at Lincoln Laboratory and within the DoD, notably since the same Executive Order tasked the federal government with implementing ZT security in its networks.
Assistant cyber division leader Jeffrey Gottschalk described a study the Laboratory conducted for the government to define ZT and approaches for deploying this type of architecture across information technology (IT) systems. Sandeep Pisharody, a researcher in the Cyber Operations & Analysis Technology Group, then discussed the unique challenges of deploying ZT to operational technology, an umbrella term for systems that interact with the physical world, ranging from mail sorting systems used by the U.S. Postal Service to the Air Force’s F-16s. "Our work is cut out for us," Pisharody says. "Because of the highly varied operational environments and proprietary building blocks of these systems, ZT implementations that focus on enterprise IT systems can’t be broadly leveraged. We must develop custom, mission-focused ZT requirements and capabilities."
Nathan Burow of the Secure Resilient Systems and Technology Group presented a new technology applying ZT principles to improve the security of operating systems, whose structure he describes as monolithic. “Imagine several gems at the center of a maze, where the gems represent secrets an adversary wants and the maze represents cyber defenses around them. Currently, a vulnerability in any part of the operating system — any path through the maze — compromises them all. Instead of one maze holding all the gems, let’s compartmentalize and put a maze around each gem, thereby forcing an attacker to win many times.”
To achieve this vision, Burow and a team have developed an approach that divides an operating systems’ code and data into separate compartments, with access-control checks in between. Each compartment is designed for least privilege, which gives users access only to the data they need for a particular task. The team expects that this technology would solve the most common vulnerabilities experienced by the Linux operating system — used widely across DoD systems — in the past five years.
Another effort is similarly applying least privilege to data access. Tyler Kaczmarek, a researcher in the same group, started his talk by pointing to the dozens of data breaches covered in the news. "The problems are bulk encryption and unnecessary privilege. Once you're in, you're in. There's no limit to what can be done to data once access is granted." His vision is to move from network-centric to data-centric security by putting data into secure, encrypted data capsules, which "self-protect the data at the atomic level," he says. Each capsule enforces access-control policies written into it that restrict both who can access the data, as well as what can be done to the data once access is granted, and logs every interaction with the data, such as who has acted on it and what was done with it. The technology is now being transitioned to the Air Force Rapid Capabilities Office.
Empowering cybersecurity analysts
John Holodnak of the AI Technology and Systems Group presented a new tool that classifies encrypted network traffic to help security analysts identify suspicious activity. As encrypted data packets are sent through the network, the tool analyzes the traffic in short time snippets to extract unique features in the signal. These features are then used to train an artificial intelligence model to predict the type of activity (e.g., file transfer, video streaming). Other technologies today can only analyze encrypted traffic to alert analysts of broadly unusual activity; this tool is unique in its ability to label the type of activity, which can help inform a response strategy. The tool also quantifies the model’s level of certainty in its prediction, a transparency that most encryption-analysis tools currently lack.
"As encrypted network traffic becomes increasingly prevalent, cyber network operators are operating without knowledge of the kinds of traffic flowing through their networks. Our tool promotes situational awareness," Holodnak says.
Another technology is using machine learning to help cyber red teams focus on securing the most relevant vulnerabilities in DoD systems. Currently there is a database of over 175,000 known vulnerabilities, each of which is manually scored for severity. Red teams, which emulate what a real attacker might do to infiltrate a system, use these scores to decide which to target. "But research has shown adversaries have gotten privy to the severity scores, and they now prioritize attacking lower scores since they are less likely to be patched," says Kenneth Alperin, who leads this work also out of the AI Technology and Systems Group.
Alperin's team created a method leveraging machine learning and natural language processing to generate more accurate and customized risk scores to inform red team priorities. Their methodology takes into account specific attacker "profiles" that can be customized, so that red teams get results tuned to the adversary of interest. Now deployed, the technology is providing significant time savings for red team assessments.
Seeing new perspectives
Throughout the two-day event, keynote speakers shared perspectives from government agencies on key cyber threats.
Neal Ziring, technical director of the Cyber Security Directorate at the National Security Agency (NSA), discussed challenges he predicts will be prevalent in this decade and strategies to address them. According to Ziring, the cybercrime ecosystem has matured, no longer resembling hacker culture but instead business culture, more organized and resilient to takedowns. The “blast radius” of attacks is creating a ripple effect because of interdependencies. National security systems’ increasing use of cloud services is creating more points of exposure.
Working together in this modern threat landscape will be crucial. “There are lots of different players in cyberspace, each of whom have different visibility into cyber activity. No one aperture is enough —we need to put all apertures together,” he says, calling for a joint capability to share data and make analysis results available quickly.
The community would also do well to support organizations "under the cybersecurity poverty line," he says. "How does a 50-person company protect themselves from a foreign government? We have to defend them by acting as one and scaling cyber solutions outward."
Lieutenant General Timothy Haugh, who commands 44,000 personnel in the Sixteenth Air Force, spoke to the challenges of defending the U.S. Air Force global network. Other featured speakers included Michael Clark, who serves as deputy director for plans and policy for the U.S. Cyber Command; Robert J. Runser, who leads the research directorate at NSA; and Brigadier General Paul Stanton, who is the commanding general of the U.S. Army Cyber Center of Excellence.
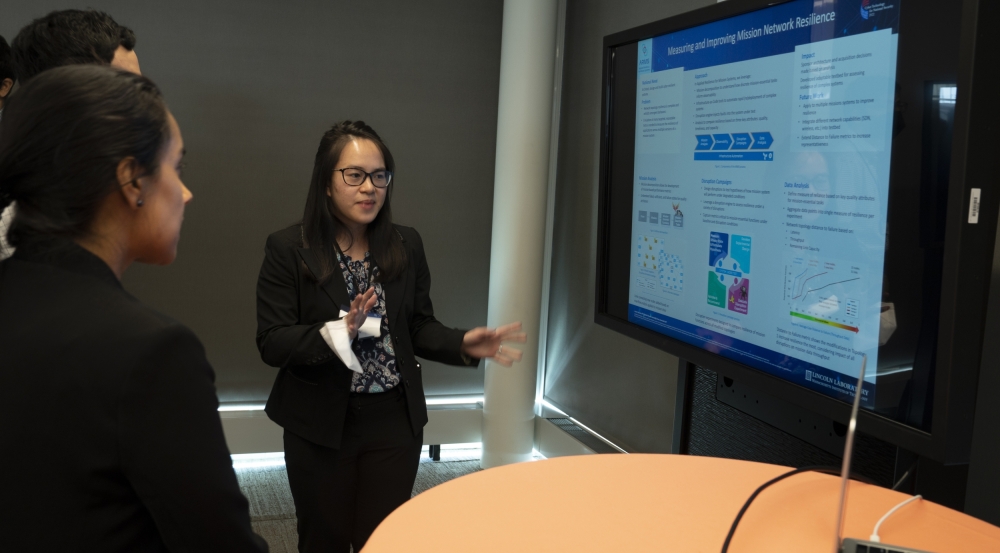
The conclusion of each day's planned agenda opened opportunities for participants to network, hear lightning talks and poster presentations, and attend two short courses on ZT security and dynamic analysis of software programs.
The CTNS organizers note that they have received positive feedback since the event, with one attendee remarking that "the knowledge of the speakers and attendees was spectacular" and that the conference was "one of the best we attended."
"We gained a better understanding of how the government deals with cyber threats and where they need the most help,” Stetson says. “We always hope our attendees take away a better understanding of the technology advances occurring at Lincoln Laboratory and how these advances can be applied to solve the problems they face in a contested cyber domain. We hope to see even more people next year!"
CTNS 2023 will take place from May 30 to June 1. For more information, please contact [email protected].