Projects

lidar
Measuring Subsurface Ocean Properties from the Air
A sensor capable of rapidly collecting high-resolution data on ocean temperature, salinity, and sound speed remotely could improve forecasting for defense missions.
Tags
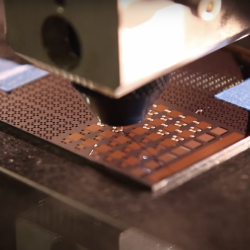
Low-Temperature Additive Manufacturing of Glass
An innovative approach to additive manufacturing of multimaterial glass items precludes the need for costly high-temperature processing techniques.
Tags

KREMS Technology Rearchitecting
A complete rearchitecting of radar backends will enable the missile and space missions on Kwajalein for decades to come.
Tags

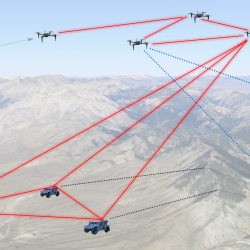
Secure Radios for Uncrewed Systems
A security module, pre-certified by the National Security Agency, for protecting communications on uncrewed platforms can accelerate the fielding of new systems and open opportunities for the commercial sector.
Tags
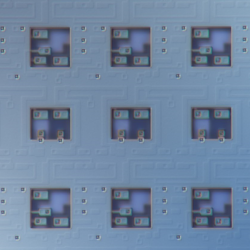
Superconducting Content-Addressable Memories (SuperCAMs)
Unconventional memory circuits can accelerate data processing in cyber sensing devices by reducing the latency of matching complex data patterns to specialized processing pipelines.
Tags
Precision Clock Synchronization for Advanced Sensing
Combined quantum networking and lasercom optical signaling techniques could impact advanced sensing applications such as geolocation with distributed systems.
Tags

Portable Aircraft-Derived Weather Observation System
A low-cost technology can increase the number and quality of wind and temperature atmospheric observations made by aircraft to improve forecasts.
Tags

Low-Cost Methane Sensor Network
Deploying large networks of ground-based methane detectors could help detect pipeline leaks, improve climate models, and regulate emission sources.
Tags

Networking for a New Era of Global Satellite Connectivity
Large constellations of satellites in low Earth orbit (LEO) allow for unparalleled global coverage but require new networking approaches.
Tags

Mitigating cellular network congestion through adaptive beamforming with reflectarrays
A low-cost, reconfigurable radio receiver architecture provides an alternative approach to filter out unwanted transmissions in millimeter-wave (MMW) signals.
Tags