Space Systems Cyber-Resiliency
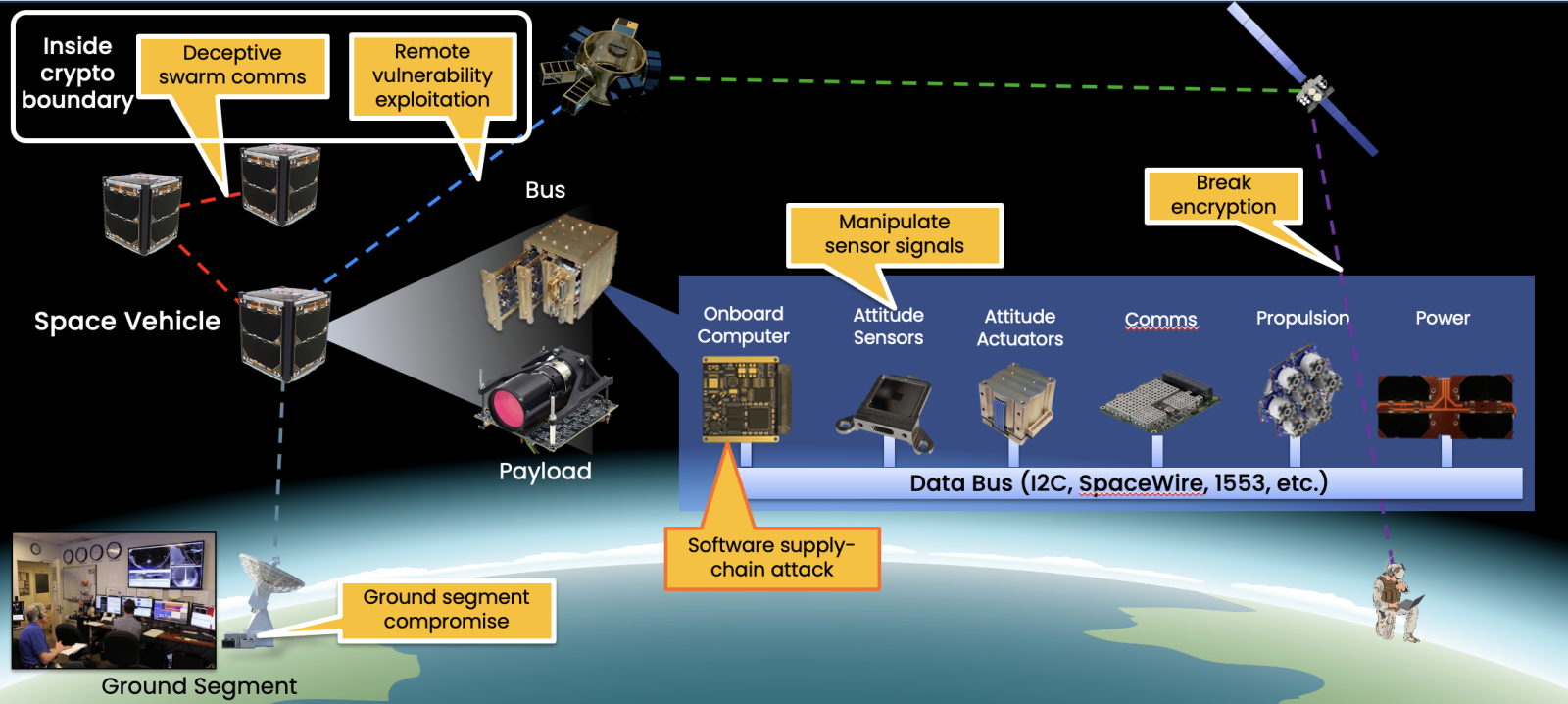
Space systems play a critical role in Department of War (DoW) and Intelligence Community (IC) operations, including communications, intelligence collection, navigation, and missile warning. Unfortunately, space-based platforms have not historically prioritized hardening against cyberattack. This is due in part to the perceived safety of their remote nature and closely protected waveforms, and in part due to strict engineering requirements that satellites must be developed under (e.g., size, weight, radiation hardening, and power). These constraints often leave little room or budget for building cyber defenses. Historical efforts have instead focused on securing the interfaces between the satellite and the outside world by leveraging cryptographic protections on data links. While this has been sufficient in the past, the capabilities of modern adversaries are rapidly evolving and may soon threaten satellite subsystems within this protected perimeter (e.g., via software supply chain attacks during production, or malware in ground segments). This gap must be closed in future systems, and mitigated in existing on-orbit platforms wherever possible.
The space systems cyber-resiliency (SSCR) initiative is addressing this gap by prototyping a suite of secure-by-design software systems that are tailored to the unique constraints of the space domain. Our goals are to harden critical satellite components against cyberattack, render them able to autonomously recover from such an attack, and enable on-orbit programmability to ensure that the system can be future-proofed against evolving threats. SSCR draws on, and seeks to develop, revolutionary technologies from many fields of computer science and aerospace, including formally verified code, real-time operating systems, cryptography, hardware design, avionics, and testbed development.
SSCR seeks to pave the way for DoW and the IC space systems that deter cyberattack by making it a costly option with limited impact. By continuously raising the bar for attackers, we hope to force them to rely on more conventional attack vectors that are easier to detect and easier to attribute, and for which we already have mature defensive capabilities.
Related
Holding the high ground: defending satellites from cyber attack